Data Management
At Oath Systems, our expertise in data management shines through. We thoroughly analyze the distinct characteristics of every business’s data infrastructure, tailoring solutions that align with the goal of safeguarding and optimizing data. Our focus is on reducing disruptions in business application availability. Our services encompass the design, construction, and oversight of smart, adaptable, and fortified data infrastructures, whether on-site or in the cloud. This approach empowers us to securely store critical data, create backups, and establish disaster recovery measures, ensuring data integrity and availability.
Our experienced engineers deploy the appropriate mix of tools, including storage consolidation with archiving, disaster recovery, and periodic backup policies.
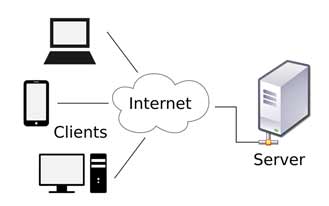
Server
Any server, network computer, software, or device that handles client queries (see client-server architecture). For instance, a Web server on the World Wide Web is a computer that utilizes the HTTP protocol to transmit Web pages to a client’s computer in response to a client request. A print server controls one or more printers on a local area network and prints documents that are sent to it by client devices. Additional examples of servers include file servers. File servers allow users to share information across a network without the need to physically transfer files via USB, or any other storage device. It’s simply a computer that can be used to provide information and software to customers, employees, and other computers.
Cloud
A simple cloud server definition is that cloud servers are virtual (not physical) servers running in a cloud computing environment that can be accessed on demand by unlimited users. Cloud servers work just like physical servers, and they perform similar functions like storing data and running applications. Because cloud services are hosted by third-party providers, they deliver computing resources over a network, most often the internet. Cloud servers are created by using virtualization software (known as a hypervisor) to divide physical servers into multiple virtual servers. A hypervisor abstracts the server’s processing power and pools it together, creating virtual servers.
How do cloud servers work?
Now that you know what a cloud server is, let’s look at how they work. Servers in the cloud function just like traditional servers, but with one key difference—they can be located virtually anywhere since they’re accessed remotely. By contrast, traditional or dedicated servers are typically hosted on-site and can only be accessed by users at that location. Also, unlike dedicated servers, cloud servers allow for the sharing of memory and processing power across linked (virtual) servers. Given their access to server space, cloud servers can be used to power every type of cloud computing delivery model, including Infrastructure as a Service (IaaS), Platform as a Service (PaaS), and Software as a Service (SaaS). Cloud data servers also have all the software they need to run built-in, so there’s no need to worry about upgrades.
What's the difference between a cloud server and a traditional server?
Cloud servers function similarly to traditional servers since they both deliver processing power, applications, and storage. However, since cloud servers are remotely accessed, they’re generally more stable and secure than traditional servers. The primary difference between a cloud server and a traditional server is that a cloud server can be shared among many users over an accessible platform, often through a network such as the internet. A traditional (dedicated) server is only accessed by a given company or entity. While cloud servers perform the same functions as physical servers, cloud servers are hosted and delivered over a network rather than set up and managed on-site. Another difference between cloud servers and physical servers is that cloud servers offer unlimited computing capacity, whereas physical servers are limited to their existing infrastructure or computing capacity. When comparing a cloud versus a physical server, physical servers are typically more customizable than cloud servers and offer more processing power, extra random access memory, and access to backup power.